Definition
Referrer is the term used to describe an optional field that is transmitted via the HTTP header when a web page is requested from a server. The main function of this field is to determine which page a given user was using before landing on the current page. By doing this, it is possible to identify the “referring website” and help trace the customer journey from one website to another. Having this type of data allows website owners to offer a more personalized user experience, and also allows blocking certain users that appear to come from untrusted sites.
Browsers play a crucial role in the process whereby referrer information is transmitted. However, not all browsers can handle referrer data. It is based on size, defined by length, and limited to 4,096 bytes. A referrer that exceeds this length will only by partially transmitted in browsers like Internet Explorer, Safari, and Firefox for Android.
Referrer or referer
It is common to see this term spelled as either referrer or referer. These terms are used interchangeably, but referer is in fact a misspelling. The incorrect spelling appeared in the original documents that outlined HTTP protocols known as HTTP 1.0. The misspelling has remained in use ever since.
How it works
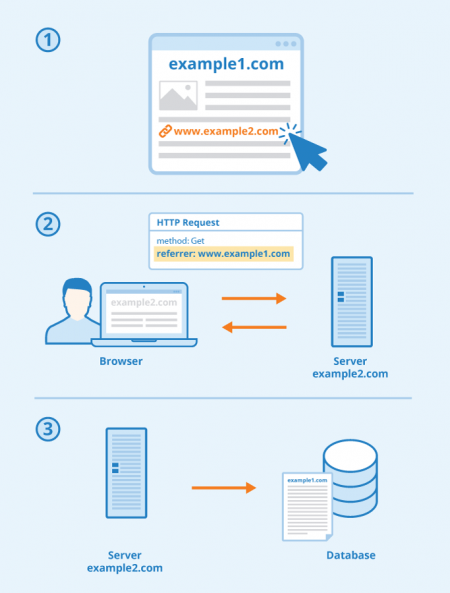
At its most basic, the HTTP referrer process works as follows:
An internet user is on web page A and clicks on a link that takes the user to web page B. The user’s web browser sends a request to the webserver that hosts web page B. The referrer (web page A) is transmitted to the server via the dedicated field on the HTTP header. The server then returns web page B and saves the referrer (web page A) to its log file.
There are certain instances in which referrer data is not transmitted to the server. These include:
- If the user visits a page by typing the URL address directly into the browser.
- If the user visits a page that was saved as a bookmark.
- A referrer transmission request may be blocked. For example, some browsers offer users the option to disable referrer headers for a more private browsing experience. This is usually done using extensions or the browser’s developer tools.
- Secure sites will not respond to the data transmission request (i.e. referrer data will not be passed on from an https site to a non-https site).
- Proxy servers can be configured to stop the browser from responding to a referrer request.
- Transmission of referrer data can be blocked through the use of a dereferrer (see point 5 below).
Benefits and criticisms
Having accurate referrer information offers website owners some advantages. This type of data plays an important role in search engine optimization. For example, it can be used to obtain a breakdown of traffic sources and subsequently to evaluate the success of affiliate links and banner ad campaigns.
Digital analytics platforms like Google Analytics feature built-in tools that can help website owners gather important referrer data. Through these platforms, it is possible to generate detailed reports that map the user’s online journey and browsing habits. This type of data can then be used to create a more personalized user experience, to boost conversion rates, or for targeted advertising purposes.
On the other hand, there are some limitations and downsides to using referrer headers. In the past, these could be used to gain insight into key user behavior, such as top keyword searches. However, for security reasons, new Google policies now withhold this type of information, and search terms entered by users will no longer be displayed in tracking systems such as Google Analytics. Instead, it says “not provided”. The only exception is paid traffic (for example traffic generated via programs like AdWords), in which case keyword information is still provided.
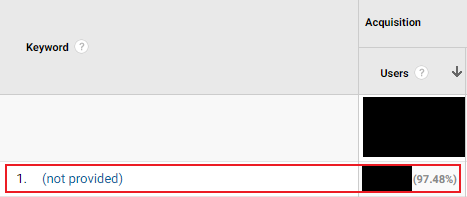
Screenshot with “not provided” of analytics.google.com
Another limitation of referrer headers is that they cannot offer a sequential view of the user journey. An internet user may reach a web page after visiting multiple websites, but referrer data does not single out which of those websites was crucial in leading a visitor to the current page. The only information transmitted is which was the URL address of the last website a user visited.
In addition, referrer information can raise privacy concerns if used without security measures. Sensitive data may be leaked to or obtained by third parties, and this information may be used with malicious intent.
What can users do to stop the transmission of the referrer?
In some cases, internet users may prefer to prevent data transmission between the browser and the server. This is often done using a dereferrer.
A dereferrer (sometimes referred to as a link anonymizer) is a service that removes the URL address of the referring website. Dereferrers can be used to increase privacy and to enable an anonymous online experience, protecting sensitive data so that they are not leaked to unwanted parties or added to server log files. Dereferrers are executed via a script or block of code, usually written in a server-side language like PHP or JavaScript. Dereferrers are also available as third-party services.
The basic process used by dereferrers involves placing a page between the referring site and the target site (i.e. the site a user is visiting after clicking on a link in the referring site). By doing so, a dereferrer manipulates HTTP requests by creating anonymous links.
Third-party dereferrer services typically allow users to prevent URL transmission by generating anonymous URLs that are later executed upon every HTTP request. This can be done through an app, or by copying and pasting a script into the website’s source code.
Alternatively, it is possible to create custom dereferrer pages. These are basic pages containing HTML code and consist of a redirect tag, a timeout script, and a redirect message. For example, someone reading a blog post about real estate in France may click on a link that will take them to another website (for example, an estate agent website). If a dereferrer is in place, the user would not be taken directly to the estate agent’s site, but would first see a page with a message saying “You are being redirected to X site”. This message would appear for a few seconds, and by placing a page in between websites, referrer headers would not be transmitted.
Related links
Similar articles
