Definition
A proxy server is a dedicated server or software system running on a computer. It acts as a gateway between a client (for example, a computer) and a server. The client is separated from the internet through the proxy server because data traffic only flows through the proxy server on its way to the requested address. The response to the request is usually sent back to the client via the same proxy server. Proxy servers offer different levels of functionality, security and data protection depending on the application, requirements or company guidelines.
How proxy servers work
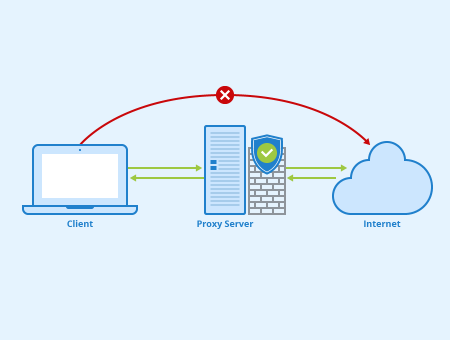
Basically, a proxy server is a computer with an IP address known to the client which acts as an intermediary between the client and a target server. No direct communication takes place between the client and the target server when using a proxy.
If the client requests a web page or a file from a server on the internet or the intranet of a company, the client’s request goes to the proxy server, which sends the request to the target server using its unique IP address. The proxy server then receives the requested data back from the target server and sends it to the requesting computer.
Application purposes of proxy servers
Depending on the configuration, proxies can perform various tasks. For example, they can be used to optimize load balancing in a network. To do this, the proxies distribute requests to a group of servers, improving capacity utilization and network performance. Proxies can also be used to control the available bandwidth.
Furthermore, a proxy server can make changes to the data sent when transmitting requests. For example, it can encrypt the data to keep it from being read during transfer.
Proxies can also speed up access to information by storing the results of user requests in the server’s cache for a specified time. This is achieved by using a caching proxy that manages a local copy of frequently requested web content. As a result, service requests can be accelerated by retrieving content from the servers’ cache if it has been previously requested by another client on the same network. In this way, a significant reduction in bandwidth usage and associated costs can be achieved.
Monitoring and filtering user requests through proxies
Proxies can be used to filter user requests and block access to certain internet content or web pages. This can be achieved by using a web proxy with content filtering. These proxies are usually used in companies or educational institutions with strict internet usage guidelines. Blocking certain websites and restricting access to certain keywords and censoring unwanted content are the basic functions of these proxies. However, certain web proxies can be used to circumvent geo-constraints and censorship rules.
Furthermore, anonymous proxy servers can be used to make online activities anonymous. This type of proxy transmits requests to a content server, hiding the client’s IP address and modifying other identifiable data such as HTTP headers. Thus, the content server does not know the identity of the source of the request. Only the proxy knows where that request comes from.
Proxies can also be used to deliver advertisements targeted to specific geographic regions. The servers verify the source IP address of the user query and determine the geographical location of the request using a GeoIP database to ensure that the ads displayed are relevant to the user’s location.
Another application of proxies is the translation of website content into the local language of the client. Responses to requests sent by local users are replaced by translated content from the source website and returned through the proxy server.
Forward proxy vs. reverse proxy
A forward proxy is the most common form of a proxy server and provides proxy services to either one or several clients. These clients often belong to a common internal network. In general, forward proxies are used to pass requests from a network to the internet via a firewall. The proxy server first checks whether a request is valid. If it isn’t, it is not transmitted by the proxy. The client then receives an error message or a forwarding address. If, however, a request is valid, the forward proxy can check whether the requested information has already been cached. Assuming this is the case, the forward proxy provides the cached information. If this is not the case, the request is sent through a firewall to a content server outside the network that returns the information to the forward proxy. The proxy, in turn, forwards this information to the client and can cache it for future requests.
A reverse proxy, on the other hand, is used to transmit requests from the internet to internal networks via a firewall. Reverse proxies can prevent internet clients from gaining direct, unmonitored access to confidential data residing on content servers in an isolated network or intranet. Like a forward proxy, a reverse proxy server first checks whether an external client’s request is valid. The processing of a request is then analogous to the procedure of a forward proxy, with the difference that if valid, requests are forwarded to an internal network and not the internet.
Possible dangers and problems when using proxy servers
Proxy servers must be configured according to their requirements and tasks. If a single port is left open during configuration, hackers can read valuable and confidential data and misuse it for their own purposes.
Besides, not all applications and target servers allow access via a proxy. Last but not least, the cache function of proxies often leads to the delivery of outdated data and website content, since the proxy always checks whether the data is stored in the cache before it transmits it to the client.
Related links
- 13 tips for optimizing your server and infrastructure for better performance
- https://www.webshare.io/blog/what-are-datacenter-proxies
- https://www.digitalcitizen.life/simple-questions-what-proxy-server-why-would-you-use-one
Similar articles
