Definition and development
Hypertext Transfer Protocol Secure (HTTPS) is a communication protocol for websites in which the encryption protocol Secure Sockets Layer (SSL) or the Transport Layer Security (TLS) encrypts the data. This enables confidential and secure data transmission on the internet. The regular HTTP layer is extended with SSL or TLS (a more recent name for the original SSL certificate). This ensures that requests from a browser and the web pages returned by a web server can be encrypted and decrypted. HTTPS thus counteracts security problems on the internet such as eavesdropping attacks or man-in-the-middle attacks. Since 2014, the use of HTTPS has officially been a ranking factor for Google and thus also of importance for search engine optimization.
HTTPS Checker
Check if your website uses HTTPS
HTTPS was first developed by the former browser operator Netscape. The reason was that regular HTTP connections were easy to intercept and thus enabled potential attackers to target individuals. This was problematic because users often transmit sensitive data using their browser windows. Valuable information such as bank connection data, emails, or credit card data requires secure protection against unauthorized access.
Today, HTTPS connections are standard on websites that work with sensitive information. Modern web browsers also identify secure and insecure connections. Browsers already indicate that if security certificates are unknown or not available, the connection may be insecure. In the future, too, the issue will become increasingly important due to digitalization and increasing cybercrime. Therefore, you should already deal with the security of your website today if you have not already done so.
Application and functionality of HTTPS
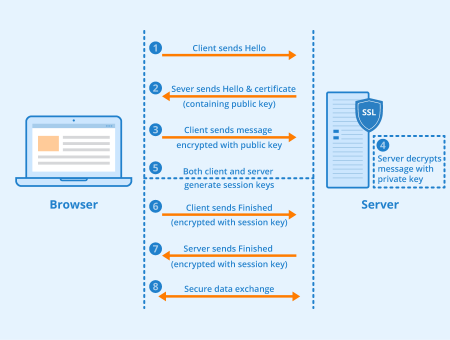
TLS/SSL, as the encryption component of HTTPS, uses certificates of the X 509 standard. This is a public key standard for creating digital certificates that allows users to authenticate senders. With these certificates, web browsers can ensure that a server actually belongs to the domain you want to access. In addition, HTTPS typically uses port 443 and not port 80, which is otherwise common for HTTP. Ports are part of a network address and allow an exact assignment of connections between client and server.
When a web page is opened, it is first encrypted with the HTTPS layer. The data forwarded from server to browser is also encrypted. Via the HTTPS sublayer of web browsers, they are then decrypted again for users, so that they can access the corresponding website as usual.
Security and limits of HTTPS
The security HTTPS can guarantee depends not only on the encryption but also on the implementation in web browsers and servers. SSL certificates are currently regarded as relatively secure, but the secure transmission of data alone is not sufficient for comprehensive protection, because data security also requires secure storage at the recipient. You should also take into account that the transmitted information is always available in decrypted form at the end system, which is why it can only be as secure as the computer used. In addition, SSL security gaps such as Heartbleed occasionally occur. Because of this serious program error, encrypted connections to private data could be read in older versions of the open-source software OpenSSL certificate.
Distinction from S-HTTP
There is a danger of confusion due to the same letters as in S-HTTP. This HTTP variant is also designed for greater security. It was developed in 1995 by the former company EIT and proposed as a standard. In terms of security, however, this version differs greatly from HTTPS encryption, which is why the two terms should not be confused.
Use and importance
Hypertext Transfer Protocol Secure is used as a standard today, especially on websites that require the input of sensitive information by users. The main areas of application are therefore online banking transactions and password-protected accounts. The latter include online shopping accounts in e-commerce, email accounts, and accounts on social networks. An attack on such accounts and the information stored there can cause great personal damage. However, some websites require the entry of personal data even without an account. Online travel agencies or providers of flights and hotels, for example, require travelers’ data to be forwarded online to the provider.
When surfing the internet users should always make sure that the websites they visit guarantee a secure connection and the protection of sensitive information. Users can easily find out about the use of HTTP Secure by looking for “https://” at the beginning of the address line in their web browsers. In most cases, the secure protocol is also visually highlighted by a small padlock symbol:
Screenshot with visually highlighted secure protocol from seobility.net
Importance in SEO and further advantages and disadvantages
In August 2014, the search engine operator Google published a blog post highlighting the use of HTTP Secure as a ranking factor. This is one of the rare cases in which Google has officially confirmed that a certain procedure has a positive effect on the position of a web page in search result pages (SERPs). Google recommends that any website that deals with sensitive information should use HTTP Secure and, if necessary, switch to HTTP Secure.
Apart from this positive effect on the ranking of a website, another advantage of HTTP Secure is that it does not require the installation of additional software. The application is therefore available to every website operator. In addition, using HTTPS increases the trust of visitors and potential customers because the abbreviation “https” in their web browsers signals a secure connection.
Compared to the security advantages, the disadvantages are rather small. Note that SSL encryption incurs additional costs for security certificates.
In summary, you can see that HTTPs has barely any disadvantages and that the transmission protocol should, therefore, be used at all costs, especially due to its relevance for search engine optimization.
If you want to switch your website to HTTPS but don’t know how to do it, we recommend this HTTPS migration guide on our blog.
Related links
- Switching from HTTP to HTTPS – Migration Guide – Seobility Blog
- https://www.howtogeek.com/181767/htg-explains-what-is-https-and-why-should-i-care/
